SECURITY & PROTECTIVE SERVICES
SECURITY ISN’T A SOFTWARE FEATURE
More than one million private security officers are working across the United States right now, more than twice the number of sworn public law enforcement. They stand post at hospitals, schools, stadiums, corporate campuses, gated communities, ports, transit hubs, courthouses, data centers, and critical infrastructure facilities that you would never want unprotected. They are, for most of the buildings and crowds in this country, the first and often only response.
Too many of those officers are under-trained, under-equipped, and under-supervised, and the liability arrives the moment something goes wrong. Sentinel Solutions Group applies real public-safety operational rigor to private protective services: policy and procedure that would survive a deposition, dispatch-grade technology that actually talks to local law enforcement, and training built by people who have sat both sides of the console.
Private Security Officers in the U.S.
The Size of Public Law Enforcement
U.S. Security Services Industry
CHALLENGE
Security programs are often stitched together from disconnected systems, an access platform from one vendor, a VMS from another, guard-tour software somewhere else. Generic IT firms treat security tech like ordinary enterprise software and miss the operational realities: how incident reports feed investigations, how credential revocation actually works in a crisis, how guard rosters align with risk posture. Sentinel brings security operations discipline and technology governance to the same engagement. We assess your platform stack, rationalize vendor contracts, design integration that actually serves the security mission, and build the governance that keeps your program defensible to leadership, regulators, and, when it matters, the courtroom.
THE SECURITY REALITY

CHALLENGE
COMMON CHALLENGES
OUR APPROACH
CORE CAPABILITIES
Security & protective services span risk assessment, technology architecture, command, response, and after-action. Most firms work one slice; we work the stack. This signature is how we see the full protective posture.
Three ongoing services that keep a security program operational, not decorative. Access control and surveillance kept current, threats identified before they become incidents, and SOC workflows tuned to reduce false positives and sharpen real signal.
Oversight of access control, surveillance, and alarm systems across facilities and perimeters.
Structured threat identification, monitoring, and response protocols built for the environment being protected.
Refinement of SOC monitoring and response workflows to reduce noise, sharpen signal, and shorten response.
OUR PRACTICES
Every Sentinel engagement is governed by proprietary practices built for the realities of security technology, access control, video, GSOC operations, and executive protection, not borrowed from commercial IT playbooks.
PROGRAM MANAGEMENT
How we govern programs.
PMP-disciplined program governance structured for political visibility, audit defensibility, and multi-administration continuity. Every milestone, deliverable, and decision gate is designed for the public-sector reality, where council turnover, budget cycles, and federal funding rules shape the timeline more than any vendor’s project plan.
CHANGE MANAGEMENT
How we prepare your people.
Organizational change management built for the GSOC desk, the guard post, and the executive protection detail, not the corporate campus. We design adoption strategies informed by shift schedules, union dynamics, civil service rules, and the operational reality that your systems cannot go dark for training. When the new security program goes live, the people behind the console are ready.
CONFIGURATION AUTHORITY
How we own the configuration.
Configuration authority for access control, camera management, and visitor management systems. Sentinel owns the foundational decisions around access levels, badge hierarchies, camera retention posture, and visitor workflows, producing the Blueprint, training, and administrator documentation that stands up to investigation, audit, and internal review.
VALUE ASSURANCE
How we prove the value.
Post-deployment governance for your physical security and protective technology investment. Sentinel independently measures whether access control, surveillance integration, and incident response outcomes specified at procurement are being realized in live operational conditions.
After engagement closes, Sentinel Sustain keeps the practice active across the life of the investment. Three tiers: Core, Active, and Strategic.
Learn more →DEEP EXPERTISE
PITFALLS TO AVOID
01
02
03
04
05
06
YOUR TEAM

MANAGING PARTNER · ENGINEERING & TECHNOLOGY
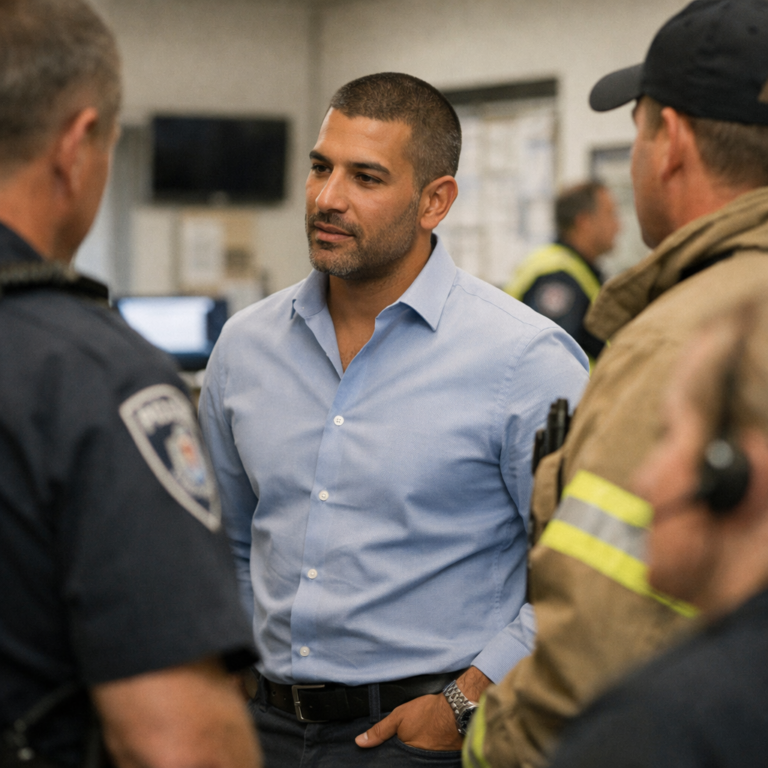
LAW ENFORCEMENT, CORRECTIONS & CAMPUS SAFETY ADVISORY
The right engagement depends on where the program is in the lifecycle. Each tier has its own scope discipline and its own deliverable cadence.
End-to-end managed operations for the access control, video, intrusion, and command-center infrastructure Sentinel helped you deploy. Sustainment, vendor coordination, version-upgrade discipline, and 24/7 incident response from the SOC. The badge is still working at the door at midnight, because someone is still accountable for the integration.
We govern the program. We never sell the platforms.
Read moreOngoing retainer with quarterly governance reviews, pre-decision advisory, and an open line for executive protection coordination, threat-assessment cycles, and vendor escalations. The program has independent counsel on the technology side of the table, before the next protective detail, the next site rollout, or the next contract cycle.
Sentinel documents. We do not litigate.
Read moreAnchored to one of SDF, SRM, SDB, or SVA. Best when the program knows which discipline is needed: an access-control modernization, video-management change readiness, configuration authority on the command center, or post-deployment outcome governance. Fixed scope, named practice, defined deliverables.
Independent. Practitioner-led. Vendor-neutral.
Explore subscriptionsA specialized service plus a signature practice plus Sentinel Institute training, packaged as a single integrated engagement. For programs standing up a new protective services technology stack from scratch and building the institutional capacity to operate it across multiple sites.
Cutting-edge. Never bleeding-edge.
Read moreREADY TO STRENGTHEN YOUR PROGRAM?